Security
Data Sovereignty and Security: Building Trust in India’s Connected Ecosystem
The Internet of Things (IoT) in India has crossed a critical threshold. We are no longer in the era of pilot projects and niche smart g...
Cybersecurity is a Manufacturing Metric: Protecting Your IP in the Age of Connected Production
For decades, the metrics that defined manufacturing excellence were physical and financial: Overall Equipment Efficiency (OEE), yield, ...
The Sovereign Cloud Edge: How India’s Data Localization Mandate is Creating a $10B Hardware Opportunity
For senior executives navigating India's digital economy, a profound shift is redefining where and how data must live. The mandate for ...
IoT Security as a Boardroom Priority: Navigating India’s New Cyber Insurance and Compliance Landscape
A chilling new reality is settling into boardrooms across India: the smart factory floor, the connected hospital, the fleet of delivery...
Building the Unbreakable Home: A Senior Executive’s Framework for Integrated Physical and Cyber Security
As a senior executive, you understand that assets must be protected. You’ve invested in robust financial controls, legal safeguards, an...
Enhancing Security in Embedded Devices for Safety
Embedded devices are ubiquitous. These items, ranging from smartwatches to appliances to automobiles, are becoming more prevalent. Howe...
Cryptocurrency Hardware Wallets For Secure Storage
Wallets have grown from a fundamental leather bag to a sophisticated and svelte piece of technology with increased capacity. They may b...
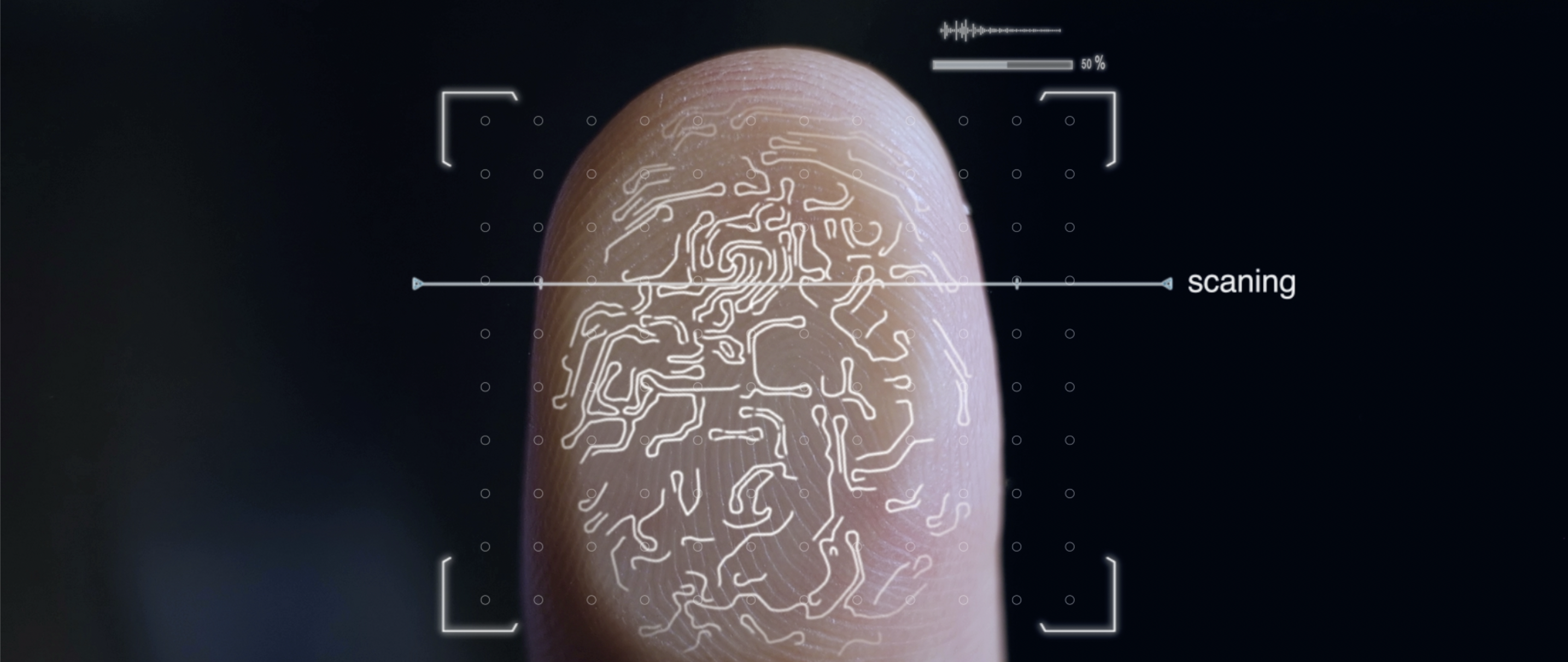
Biometric Access Cards: Your Identity is in the Safe Hands
Biometric Access Cards: Your Identity is in the Safe HandsBiometric access cards are gaining popularity for usage at airports and high-...
Biometric fingerprint access cards to bring security to a workplace
Employees are growing more dependent on their gadgets and the information they deliver as technology is increasingly used in the workpl...