Blog
Quantum-Safe IoT: Preparing India’s Critical Infrastructure for the Next Decade
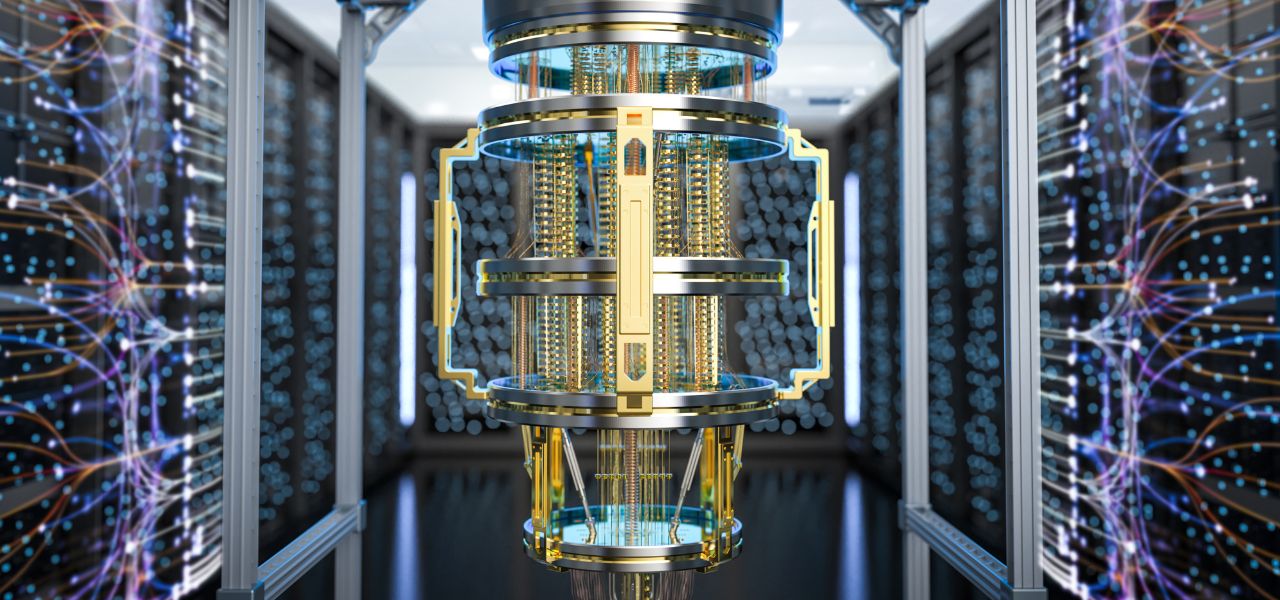
A silent countdown has begun in the basements of research labs and intelligence agencies worldwide. While quantum computing promises to revolutionize medicine and materials science, it also poses an existential threat to the digital security foundations of our modern world. For India’s leaders overseeing power grids, financial networks, defense systems, and smart cities, a daunting new question has emerged: What happens when a quantum computer, perhaps a decade from now, can break the encryption protecting our most critical IoT infrastructure in minutes?
This is not science fiction. It is a mathematical inevitability known as “Q-Day”—the day when scalable quantum computers can crack the public-key cryptography (like RSA and ECC) that secures every digital handshake, from your UPI transaction to the command controlling a smart substation. For the IoT devices embedded in India’s critical infrastructure, with lifespans of 15-20 years, the threat is not future; it is present. The decisions made today about which chips to embed and which protocols to deploy will determine national security and economic resilience in the quantum era.
This is the imperative of Quantum-Safe IoT: engineering connected systems today that will remain secure tomorrow, against both classical and quantum attacks. For the CISO, CTO, and strategic planner, this is a rare challenge—a long-term threat requiring immediate, strategic investment.
The Quantum Threat: Decrypting Today’s Secrets, Forging Tomorrow’s Commands
The danger is twofold:
- Store Now, Decrypt Later (Harvest Today): A sophisticated adversary can intercept and store encrypted IoT data today—be it sensitive telemetry from a gas pipeline or encrypted firmware updates for railway signaling. They wait. When a quantum computer becomes available, it will decrypt this historical trove, gaining years of intelligence.
- Break and Imitate (Attack Tomorrow): In the future, an attacker could break the cryptographic signature of a legitimate control command, forge a malicious one, and take over critical infrastructure in real-time.
The vulnerability lies in the very devices forming India’s digital backbone: smart meters, SCADA systems, traffic management controllers, and industrial sensors deployed today with 10-20 year lifespans, but cryptography with a shelf life of perhaps 5-10 years.
The Quantum-Safe Solution: Building Crypto-Agile Systems
“Quantum-safe” or “post-quantum” cryptography (PQC) refers to new cryptographic algorithms designed to be secure against both classical and quantum computer attacks. The global standardisation race, led by NIST (National Institute of Standards and Technology), is nearing completion.
However, for IoT, the challenge is profoundly harder than for IT systems. It’s not a simple software patch. It demands a full-stack, hardware-up architectural rethink due to IoT’s unique constraints:
- Limited Compute: PQC algorithms are more computationally intensive.
- Constrained Power: Many devices have been battery-powered for years.
- Long Lifecycles: Devices in the field cannot be easily recalled.
- Diverse Ecosystem: Millions of heterogeneous devices from various vendors.
The Strategic Framework: A Four-Pillar Migration Plan for India
For leaders of critical infrastructure entities, the path to quantum resilience must be systematic and begin now.
Pillar 1: Crypto-Inventory & Risk Assessment
You cannot protect what you do not know.
- Action: Conduct a thorough cryptographic inventory of your IoT estate. Map every device, its cryptographic implementation (algorithm, key length, library), its function, and the sensitivity of the data it handles or commands it executes.
- Outcome: A prioritized risk matrix. Which systems, if compromised, would cause catastrophic failure (e.g., grid control)? Which have the longest deployment horizons? These become migration Priority 1.
Pillar 2: The “Crypto-Agile” Hardware Mandate
The core of the solution. Crypto-agility is the ability for a system to seamlessly update its cryptographic algorithms without needing to replace the hardware.
- Action: Mandate that all new IoT procurements and deployments must be crypto-agile. This is not a software feature; it is a hardware specification.
- Implementation: This requires devices built with:
- Sufficient Headroom: Microcontrollers with 2-4x the compute power and memory of today’s minimal needs to run future PQC algorithms.
- Secure Key Storage: Hardware Security Modules (HSMs) or Secure Elements that can store and manage new types of PQC keys.
- Field-Upgradable Firmware: Secure, robust Over-The-Air (OTA) update mechanisms with rollback protection.
Pillar 3: Hybrid Implementation & Pilot Deployment
A “big bang” switch is impossible. A phased, hybrid approach is essential.
- Action: Initiate pilot projects using hybrid cryptography. This means running a traditional algorithm (e.g., ECDSA) and a new NIST-standardized PQC algorithm (e.g., CRYSTALS-Dilithium) together for digital signatures.
- Outcome: The system remains secure if one algorithm is broken. Pilots in non-critical but significant systems (e.g., a city’s water quality monitoring network) build organizational expertise and test performance impact before scaling to national grids.
Pillar 4: National Standards & Ecosystem Development
This is a national security issue that requires public-private collaboration.
- Action: Advocate for and participate in the development of Indian standards (through BIS) for quantum-safe IoT. Support the creation of testing and certification labs for PQC hardware.
- Outcome: A sovereign, trusted supply chain for quantum-resilient critical infrastructure components, reducing dependence on foreign vendors for core security.
The Cionlabs Imperative: Engineering the Crypto-Agile Device
We are pioneering the hardware foundation for this transition. Our work focuses on making crypto-agility a practical, deployable reality for Indian infrastructure.
- Quantum-Safe Hardware Architecture: We design system-on-chip (SoC) architectures and select components that provide the necessary performance headroom and secure key storage for PQC migration paths.
- Firmware for the Future: We develop modular cryptographic firmware where algorithms can be swapped via secure OTA updates, implementing hybrid schemes for gradual transition.
- Performance & Power Optimization: We specialize in tailoring PQC implementations for constrained IoT environments, ensuring security doesn’t cripple battery life or responsiveness.
The Leadership Calculus: The Cost of Inaction Versus Investment
The business case is one of risk mitigation versus strategic cost.
- Cost of Proactive Migration: A 15-25% premium on hardware today for crypto-agile design. Investment in pilot programs and staff training.
- Cost of Reactive Catastrophe: In a decade, a forced, emergency recall and replacement of millions of embedded devices across a national power grid or transport network. The financial, operational, and national security costs would be incalculable.
For the board, this is a classic “pay a little now or a fortune later” scenario, but with stakes that include national stability.
Conclusion: Building the Digital Fortress for the Next Era
The quantum threat to IoT is unique. It is a certainty on the horizon, not a probability. The IoT devices we are cementing into our national infrastructure today are the very assets that will be most exposed when Q-Day arrives.
India has a historic opportunity. By acting now, we can avoid the frantic, vulnerable scramble that other nations will face. We can engineer sovereign, quantum-resilient critical infrastructure that becomes a global benchmark for security and foresight.
The mandate for leaders is clear: begin the cryptographic transition now. Treat every new IoT deployment as a 20-year security decision. Invest in crypto-agility. The decisions made in boardrooms and government committees today will determine whether India’s digital infrastructure stands firm or crumbles in the quantum dawn. The decade to prepare is already underway.
Ready to future-proof your critical IoT infrastructure against the quantum threat?
Contact Cionlabs to design and deploy crypto-agile, quantum-safe hardware systems that secure today’s operations against tomorrow’s attacks.